What is the National Cybersecurity Strategy? A cybersecurity expert explains what it is and what the Biden administration has changed
Published in Business News
The Biden administration released its first National Cybersecurity Strategy on March 2, 2023. The last version was issued in 2018 during the Trump administration.
As the National Security Strategy does for national defense, the National Cybersecurity Strategy outlines a president’s priorities regarding cybersecurity issues. The document is not a directive. Rather, it describes in general terms what the administration is most concerned about, who its major adversaries are and how it might achieve its goals through legislation or executive action. These types of strategy statements are often aspirational.
As expected, the 2023 Biden National Cybersecurity Strategy reiterates previous recommendations about how to improve American cybersecurity. It calls for improved sharing of information between the government and private sector about cybersecurity threats, vulnerabilities and risks. It prescribes coordinating cybersecurity incident response across the federal government and enhancing regulations. It describes the need to expand the federal cybersecurity workforce. It emphasizes the importance of protecting the country’s critical infrastructure and federal computer systems. And it identifies China, Russia, Iran and North Korea as America’s main adversaries in cyberspace.
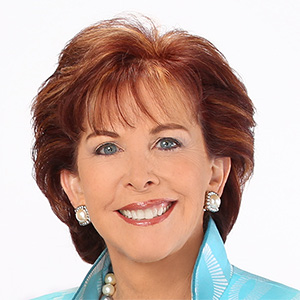
However, as a former cybersecurity industry practitioner and current cybersecurity researcher, I think that the 2023 document incorporates some fresh ideas and perspectives that represent a more holistic approach to cybersecurity. At the same time, though, some of what is proposed may not be as helpful as envisioned.
Some of the key provisions in the current National Cybersecurity Strategy relate to the private sector, both in terms of product liability and cybersecurity insurance. It also aims to reduce the cybersecurity burden on individuals and smaller organizations. However, I believe it doesn’t go far enough in fostering information-sharing or addressing the specific tactics and techniques used by attackers.
For decades, the technology industry has operated under what is known as “shrink-wrap” licensing. This refers to the multiple pages of legal text that customers, both large and small, routinely are forced to accept before installing or using computer products, software and services.
While much has been written about these agreements, such licenses generally have one thing in common: They ultimately protect vendors such as Microsoft or Adobe from legal consequences for any damages or costs arising from a customer’s use of their products, even if the vendor is at fault for producing a flawed or insecure product that affects the end user.
In a groundbreaking move, the new cybersecurity strategy says that while no product is totally secure, the administration will work with Congress and the private sector to prevent companies from being shielded from liability claims over the security of their products. These products underpin most of modern society.
Removing that legal shield is likely to encourage companies to make security a priority in their product development cycles and have a greater stake in the reliability of their products beyond the point of sale.
In another noteworthy shift, the strategy observes that end users bear too great a burden for mitigating cybersecurity risks. It states that a collaborative approach to cybersecurity and resiliency “cannot rely on the constant vigilance of our smallest organizations and individual citizens.” It stresses the importance of manufacturers of critical computer systems, as well as companies that operate them, in taking a greater role in improving the security of their products. It also suggests expanded regulation toward that goal may be forthcoming.
Interestingly, the strategy places great emphasis on the threat from ransomware as the most pressing cybercrime facing the U.S. at all levels of government and business. It now calls ransomware a national security threat and not simply a criminal matter.
The new strategy also directs the federal government to consider taking on some responsibility for so-called cybersecurity insurance.
Here, the administration wants to ensure that insurance companies are adequately funded to respond to claims following a significant or catastrophic cybersecurity incident. Since 2020, the market for cybersecurity-related insurance has grown nearly 75%, and organizations of all sizes consider such policies necessary.
This is understandable given how many companies and government agencies are reliant on the internet and corporate networks to conduct daily operations. By protecting, or “backstopping,” cybersecurity insurers, the administration hopes to prevent a major systemic financial crisis for insurers and victims during a cybersecurity incident.
However, cybersecurity insurance should not be treated as a free pass for complacency. Thankfully, insurers now often require policyholders to prove they are following best cybersecurity practices before approving a policy. This helps protect them from issuing policies that are likely to face claims arising from gross negligence by policyholders.
In addition to dealing with present concerns, the strategy also makes a strong case for ensuring the U.S. is prepared for the future. It speaks about fostering technology research that can improve or introduce cybersecurity in such fields as artificial intelligence, critical infrastructure and industrial control systems.
The strategy specifically warns that the U.S. must be prepared for a “post-quantum future” where emerging technologies could render existing cybersecurity controls vulnerable. This includes current encryption systems that could be broken by future quantum computers.
While the National Cybersecurity Strategy calls for continuing to expand information-sharing related to cybersecurity, it pledges to review federal classification policy to see where additional classified access to information is necessary.
The federal government already suffers from overclassification, so if anything, I believe less classification of cybersecurity information is needed to facilitate better information-sharing on this issue. It’s important to reduce administrative and operational obstacles to effective and timely interaction, especially where collaborative relationships are needed between industry, academia and federal and state governments. Excessive classification is one such challenge.
Further, the strategy does not address the use of cyber tactics, techniques and procedures in influence or disinformation campaigns and other actions that might target the U.S. This omission is perhaps intentional because, although cybersecurity and influence operations are often intertwined, reference to countering influence operations could lead to partisan conflicts over freedom of speech and political activity. Ideally, the National Cybersecurity Strategy should be apolitical.
That being said, the 2023 National Cybersecurity Strategy is a balanced document. While in many ways it reiterates recommendations made since the first National Cybersecurity Strategy in 2002, it also provides some innovative ideas that could strengthen U.S. cybersecurity in meaningful ways and help modernize America’s technology industry, both now and into the future.
This article is republished from The Conversation, an independent nonprofit news site dedicated to sharing ideas from academic experts. Like this article? Subscribe to our weekly newsletter.
Read more:
Local governments are attractive targets for hackers and are ill-prepared
The FBI is breaking into corporate computers to remove malicious code – smart cyber defense or government overreach?
Richard Forno has received research funding related to cybersecurity from the National Science Foundation (NSF) and the Department of Defense (DOD) during his academic career, and sits on the advisory board of BlindHash, a cybersecurity startup focusing on remedying the password problem. He is CoPI of UMBC's Scholarship-for-Service program, which is referenced in the 2023 National Cybersecurity Strategy.








Comments