Current News
/ArcaMax
25 years later, a Columbine teacher reflects on why she stayed: “We take care of each other”
DENVER — Twenty-five years ago, Michelle DiManna sat in the math office at Columbine High School grading papers and talking to a colleague when she heard students screaming in terror.
Two heavily armed shooters had entered the Jefferson County school late in the morning on April 20, 1999, and proceeded to kill 12 of their classmates and a ...Read more
Rule for debate on war supplemental heads to House floor
WASHINGTON — The House Rules Committee approved a rule late Thursday for consideration of a $95.3 billion foreign aid package in a rare bipartisan vote that signaled solid support for the measure despite considerable GOP opposition.
The committee voted 9-3 for the rule setting terms for floor consideration of the long-stalled aid package, ...Read more
Colorado “assault” weapons ban faces likely key vote in Senate from father of mass shooting victim
The proposed ban on the sale, transfer and manufacturing of many high-powered, semi-automatic guns in Colorado will face an uphill fight in the state Senate after clearing the state House for the first time.
The measure, House Bill 1292, would ban guns referred to as “assault” weapons by its Democratic sponsors. It now heads to a Senate ...Read more
'Help me, help me': Metro bus driver stabbed, reviving fears about safety
LOS ANGELES — A video circulating on social media captured the moments a bus driver was stabbed Saturday night by a passenger in Willowbrook as other passengers watched.
The driver survived and is recovering at home, but the incident heightens concern about the safety of Metro's bus drivers and passengers. The attack came less 24 hours after ...Read more

Wild turkey numbers are falling in some parts of the US – the main reason may be habitat loss
Birdsong is a welcome sign of spring, but robins and cardinals aren’t the only birds showing off for breeding season. In many parts of North America, you’re likely to encounter male wild turkeys, puffed up like beach balls and with their tails fanned out, aggressively strutting through woods and parks or stopping traffic on your street....Read more

Getting a good night’s rest is vital for neurodiverse children – pediatric sleep experts explain why
Most of us are all too familiar with the consequences of a poor night’s sleep – be it interrupted sleep or simply too little of it. If you’re a parent with kids at home, it often leaves you and your children on edge.
Children with neurodiverse conditions, such as autism and attention-deficit/hyperactivity disorder, or ADHD, are ...Read more

Caring for older Americans’ teeth and gums is essential, but Medicare generally doesn’t cover that cost
C. Everett Koop, the avuncular doctor with a fluffy white beard who served as the U.S. surgeon general during the Reagan administration, was famous for his work as an innovative pediatric surgeon and the attention he paid to the HIV-AIDS crisis.
As dentistry scholars, we believe Koop also deserves credit for something else. To help ...Read more

South Korean President Yoon faces foreign policy challenges after the National Assembly election
South Korea’s parliamentary election of April 10, 2024, was widely seen as a referendum on President Yoon Suk Yeol’s first two years in office.
That being the case, the nation collectively expressed its strong disapproval.
With a relatively high turnout of 67%, voters handed Yoon’s conservative People’s Power Party ...Read more

How Trump is using courtroom machinations to his political advantage
The second week is wrapping up in former President Donald Trump’s first criminal trial on charges from the state of New York related to paying hush money to an adult film star. So far, the jury has been selected, but no other proceedings have begun.
The Conversation U.S. interviewed Tim Bakken, a former New York prosecutor and now a...Read more

Are tomorrow’s engineers ready to face AI’s ethical challenges?
A chatbot turns hostile. A test version of a Roomba vacuum collects images of users in private situations. A Black woman is falsely identified as a suspect on the basis of facial recognition software, which tends to be less accurate at identifying women and people of color.
These incidents are not just glitches, but examples of more ...Read more
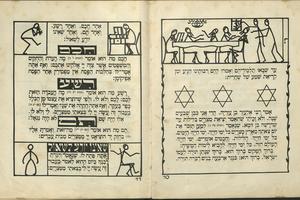
From sumptuous engravings to stick-figure sketches, Passover Haggadahs − and their art − have been evolving for centuries
The Jewish festival of Passover recalls the biblical story of the Israelites enslaved by Egypt and their miraculous escape. During a ritual feast known as a Seder, families celebrate this ancient story of deliverance, with each new generation reminded to never take freedom for granted.
Every year, a written guide known as a “...Read more
Iran acknowledges drone attack by Israel and says it failed
Iranian state media confirmed an attack by Israel in the early hours of Friday and said the “sabotage” operation involving drones had failed.
Israel launched a retaliatory strike on Iran following last week’s missile and drone barrage from Tehran, according to two U.S. officials, though media from both countries appeared to downplay the ...Read more
Ukraine says bomber downed as Russian strike leaves 9 dead
Ukraine said it shot down a Russian strategic bomber in combat for the first time since the Kremlin’s invasion began after the aircraft launched a missile strike that left at least nine people dead in the central Dnipro region.
The Tu-22M3 was downed some 300 kilometers (186 miles) from the Ukrainian border after launching missiles, Ukraine�...Read more

'I live in constant fear': Fraternity suspended after UC Davis student alleges hazing
SACRAMENTO, Calif. — Sean Tran, a first-year UC Davis student, began to blossom as he threw himself into campus culture. He experienced college life with a core group of friends and loved his environmental sciences degree program.
To further his career opportunities, Tran pledged Alpha Kappa Psi, a co-ed professional business fraternity, one ...Read more

Several dozen ships lost propulsion in Maryland waters before Key Bridge collapse: 'You're basically just drifting'
BALTIMORE — After delivering a load of sugar to the Domino refinery in Baltimore’s Inner Harbor two winters ago, a 567-foot bulk carrier departed for Georgia but didn’t get very far before experiencing engine trouble.
Not long after the Nazenin sailed underneath the Francis Scott Key Bridge, a mechanical malfunction cut the flow of ...Read more

Vulnerable Florida patients scramble after abrupt Medicaid termination
TAMPA, Fla. – Esther JeanBart leaned over her son’s wheelchair, caressing his face and trying to make him giggle. Gianni JeanBart was under the weather, but still his eyes rolled toward her and his mouth widened, cracking a smile.
Esther JeanBart said she has missed the sound of Gianni’s voice the most. In 2017, the U.S. Marine was in a ...Read more

Supreme Court tackles homelessness crisis. What that means for California
WASHINGTON — The Supreme Court is poised to hear its most important case ever on the homelessness crisis, and to decide whether cities in California and the West may enforce laws against camping on sidewalks or other public property.
Homelessness has often been cited as the most intractable problem for cities in the West, and it has grown ...Read more

Israel launches missile strikes on Iran, US officials say
Israel launched a retaliatory strike on Iran less than a week after Tehran’s rocket and drone barrage, according to two U.S. officials, but Iranian media appeared to downplay the incident in the hours that followed the initial reports.
An explosion was heard early Friday in Iran’s central city of Isfahan, the country’s semi-official Fars ...Read more

Israel launches missile strikes on Iran, US officials say
Israel launched a retaliatory strike on Iran less than a week after Tehran’s rocket and drone barrage, according to two U.S. officials, raising fears of a widening conflict across the Middle East.
An explosion was heard early Friday in Iran’s central city of Isfahan, the country’s semi-official Fars news agency reported. Nuclear ...Read more

Israel launches missile strikes on Iran, US officials say
Israel launched a missile strike on Iran less than a week after Tehran’s rocket and drone barrage, according to two U.S. officials.
An explosion was heard Friday in Iran’s central city of Isfahan, the country’s semi-official Fars news agency reported, as concerns mounted about Israeli retaliation.
Flights were suspended in Isfahan and ...Read more
Popular Stories
- How Trump is using courtroom machinations to his political advantage
- Wild turkey numbers are falling in some parts of the US – the main reason may be habitat loss
- Full jury selected for Trump hush money trial
- 'I live in constant fear': Fraternity suspended after UC Davis student alleges hazing
- Caring for older Americans’ teeth and gums is essential, but Medicare generally doesn’t cover that cost