Current News
/ArcaMax

California's Latino lawmakers choose priority bills for 2024. Here are their top issues
SACRAMENTO, Calif. — California’s Latino Caucus gathered Tuesday morning to announce its legislative priorities for 2024 — highlighting a package of bills which concentrates on the state’s undocumented immigrants.
The caucus, consisting of 35 members, is influential in the Legislature and has championed a series of wins over the last ...Read more

Supreme Court set to hear arguments over Trump immunity in Jan. 6 election interference case
The conservative Supreme Court is poised to hear oral arguments on Thursday over former President Donald Trump’s explosive claim that former presidents have blanket immunity from criminal prosecution for acts taken while in office.
The hearing marks a critical milestone as the nation waits to see if Trump will face accountability for the ...Read more
News briefs
More than 150,000 Republicans voted for Nikki Haley in Pa. primary
PHILADELPHIA — Former South Carolina Gov. Nikki Haley dropped out of the Republican presidential race in early March but still received more than 16% of the vote in Pennsylvania’s Republican presidential primary Tuesday, a sign of discontent with former President Donald ...Read more

Sharks 'adapting their movements and routines,' great white researchers discover
Do great white sharks change their behaviors in different environments, or do the apex predators follow the same routines regardless of location?
Researchers recently set out to solve this shark puzzle, as they reportedly discovered great white behaviors by attaching smart tags and cameras to their fins.
Great whites adapt their movements and ...Read more

Marine killed during 'routine military operations' at Camp Pendleton
SAN DIEGO — A Marine was killed at Camp Pendleton Tuesday evening during what military officials described as "routine military operations."
The Marine was a member of the Marine Light Attack Helicopter Training Squadron 303, Marine Aircraft Group 39, which is part of the 3rd Marine Aircraft Wing.
The 3rd Marine Aircraft Wing's ...Read more
North Carolina parent fails in effort to ban video of Native Americans talking about Thanksgiving
CARY, N.C. — A Wake County parent is trying to get a video about the Native American perspective of Thanksgiving banned from schools because she claims it’s filled with lies and is racist to white people.
The YouTube video from Cut.com shows Native Americans using words like “horror beyond measure,” “massacre,” “slaughtered,” �...Read more

Harvard students rush Harvard Yard for Palestine tent encampment; Emerson students protesting too
BOSTON — Harvard students are the latest college kids to set up a tent encampment for Palestine, as they reportedly rushed Harvard Yard to create a “liberated zone” on the Cambridge campus Wednesday.
Meanwhile in Boston, Emerson College officials were warning students of “imminent law enforcement action” because the pro-Palestine ...Read more

Navy sailor formerly stationed in Norfolk found guilty of attempted espionage
NORFOLK, Va. — A Navy chief was convicted of attempted espionage last week in a San Diego military court after he was accused of providing classified documents to a foreign contact while stationed in Norfolk and Japan.
Chief Fire Controlman Bryce S. Pedicini was found guilty of attempted espionage, failure to obey a lawful order and attempted...Read more

Arizona House votes to repeal near-total abortion ban from 1864
Arizona lawmakers Wednesday voted to repeal an unpopular near-total abortion ban that was enacted in 1864.
The Republican-controlled state house voted 32-28 to approve repealing the draconian, 160-year-old law after a handful of GOP lawmakers defected to join Democrats.
The bill now moves on to the state Senate. The GOP also narrowly controls ...Read more

Hidden ancient phallus carving discovered at Roman fort in United Kingdom -- again
Since the age of the Romans, a lot has changed.
Aqueducts have been replaced with sewer systems and indoor plumbing. Gladiator battles have been replaced by the National Football League. Even the earliest medical tools, like scalpels and forceps have, thankfully, been updated in the past few millennia.
What hasn’t changed is the desire to ...Read more

Man busted in misogynistic Manhattan attacks raved, 'You have to check women sometimes,' prosecutors say
NEW YORK — A Bronx man charged with eight random punching attacks on women since February, ranted to cops that he sometimes had to “check” women in order to keep them in line, officials say.
“It’s different with men,” Daquan Armstead, 31, told a detective after he was arrested and charged with assaulting random women in Manhattan, a...Read more

California labor tries again to get unemployment pay for striking workers. Can state afford it?
SACRAMENTO, Calif. — California labor unions are once again fighting to secure unemployment pay for striking workers after Gov. Gavin Newsom vetoed their effort last year.
But there is a looming question hanging over Senate Bill 1116 from Burbank Sen. Anthony Portantino: How will the state cover additional workers as its unemployment ...Read more

Trump is a co-conspirator in Michigan's 2020 false electors plot, state investigator says
LANSING, Michigan — Michigan prosecutors consider former President Donald Trump and some of his top aides co-conspirators in the plot to submit a certificate falsely claiming he won Michigan's 2020 election, an investigator for Attorney General Dana Nessel's office testified Wednesday in court.
Howard Shock, a special agent for Nessel, said ...Read more

Gov. Kemp signs bill outlawing property squatting in Georgia
ATLANTA — Gov. Brian Kemp signed a bill Wednesday criminalizing property squatting after a surge of reports about the practice in Atlanta and Georgia.
The governor’s approval comes amid an increase in national stories about trespassers seizing control of vacant homes, violently clashing with realtors and landlords, trashing properties, and ...Read more

Qatar will host meeting to discuss Ukrainian proposal to end war
National security advisers and senior officials from around the world are set to meet in Doha, Qatar, this weekend to discuss plans for a summit on Ukraine’s conditions for a settlement with Russia, according to people familiar with the matter.
The meeting of officials from the Group of Seven and the so-called Global South is part of a round ...Read more

3 fishermen accused of illegally transporting Alaska crab to Seattle for better prices
ANCHORAGE, Alaska — Three fishermen are facing federal charges after being accused of illegally transporting more than 7,000 pounds of crab harvested in Southeast Alaska to Seattle in hopes of getting better prices there.
Instead, federal prosecutors say, much of the haul was wasted upon arrival in Washington state because the crab had either...Read more

Donald Payne Jr., who filled father's seat in the House, dies at 65
WASHINGTON — Rep. Donald M. Payne Jr., a former Newark, New Jersey, city council president who followed his trailblazing father to Congress, has died at age 65, New Jersey Gov. Phil Murphy announced Wednesday.
“With his signature bowtie, big heart and tenacious spirit, Donald embodied the very best of public service,” Murphy said in a ...Read more
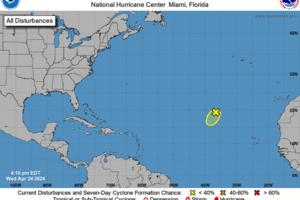
Hurricane center watching blip in Atlantic. No threat but hints at busy season ahead
MIAMI — The National Hurricane Center is already watching something in the Atlantic, and it’s only April.
The low-pressure area in question is a thousand miles away from inhabited land and expected to dissolve in the next few days, but it’s also a reminder that the upcoming hurricane season is poised to be an active one.
The season ...Read more

Gov. Gavin Newsom sent CHP officers to fight crime in Oakland. Now he's sending them to Bakersfield
Gov. Gavin Newsom announced Wednesday that he's sending California Highway Patrol officers to Bakersfield, an expansion of a law enforcement campaign launched earlier this year with an effort to tamp down crime in hard-hit California cities.
Kern County, home to Bakersfield, has higher rates of violent and property crime and more arrests ...Read more

Universal Studios tram riders were seriously injured in crash, lawyer says
LOS ANGELES — A passenger on a Universal Studios tram car that crashed into a guardrail on Saturday estimates the ride reached speeds up to 20 to 25 mph after the driver apparently lost control of the tram, which is much faster than the usual slow pace of the attraction, according to the man's attorney.
Fifteen passengers aboard the tram ...Read more
Popular Stories
- Senate approves nearly $61B of Ukraine foreign aid − here’s why it helps the US to keep funding Ukraine
- Biden signs foreign aid bill, says weapons to be sent to allies within hours
- Supreme Court sounds wary of Idaho's ban on emergency abortions for women whose health is in danger
- VIDEO: NYU pro-Gaza protesters chase NYPD chief into campus building
- Donald Payne Jr., who filled father's seat in the House, dies at 65